Who this is for: Security‑focused architects and engineering leads evaluating automation platforms for regulated, large‑scale environments.
Quick Diagnosis: Your organization needs a platform that meets strict security, compliance, and governance requirements.
- Need on‑premise control, granular IAM, and custom audit logs? → n8n
- Prefer a fully managed SaaS with built‑in SOC‑2 coverage and limited self‑service security config? → Zapier
In the field, teams often run into missing TLS hardening only when the first external audit flags it.
We cover this in detail in the n8n vs Zapier Comparison Guide.
Fast‑track security checklist
| Requirement | n8n (self‑hosted) | Zapier (cloud) |
|---|---|---|
| TLS 1.2+ encryption in transit | ✅ Configurable via reverse‑proxy (NGINX/Traefik) | ✅ Managed by Zapier |
| Encryption at rest | ✅ Disk‑level (LUKS, BitLocker) | ✅ Encrypted storage, no customer control |
| SOC 2 / ISO 27001 | ❌ Only with your own audit | ✅ Included in Zapier Enterprise |
| HIPAA / PHI | ✅ Possible with HIPAA‑ready stack | ❌ Not offered |
| GDPR / Data residency | ✅ Choose any region | ✅ EU data centers (limited regions) |
| SAML / OIDC SSO | ✅ Full SAML, OIDC, LDAP, Azure AD | ✅ SAML & OIDC (Enterprise tier) |
| IP allow‑list / VPC isolation | ✅ Network firewalls, private subnets | ✅ IP allow‑list (Enterprise) |
| Granular RBAC | ✅ Fine‑grained per‑workflow | ✅ Role groups, less granularity |
| Immutable audit log | ✅ Write‑once logs (e.g., Elasticsearch) | ✅ Event logs, limited retention |
| Secret management | ✅ Vault, AWS Secrets Manager, .env encryption | ✅ Encrypted API keys, no external store |
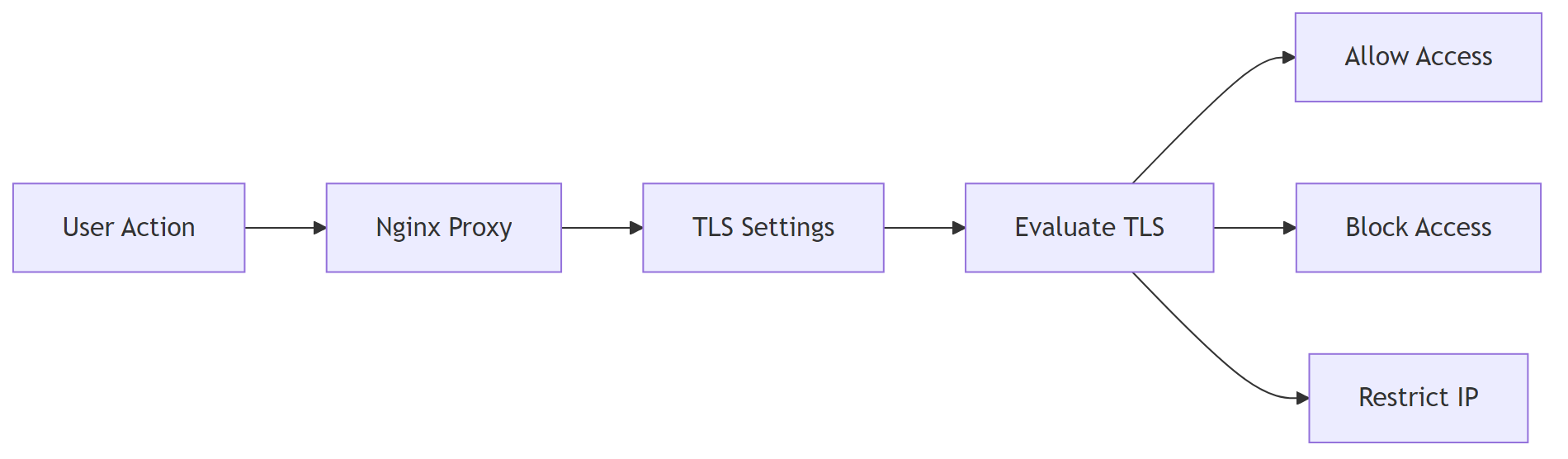
1. Enterprise‑grade Network Security
Purpose: Harden the transport layer and restrict who can reach your automation endpoint.
If you encounter any n8n vs zapier pricing cost resolve them before continuing with the setup.
1.1 TLS termination & HSTS on n8n
Use Nginx as a reverse‑proxy; enforce TLS 1.2+ and add HSTS.
# /etc/nginx/conf.d/n8n.conf – basic server block
server {
listen 443 ssl http2;
server_name automation.example.com;
# TLS settings – certificates and protocols
ssl_certificate /etc/letsencrypt/live/automation.example.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/automation.example.com/privkey.pem;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_prefer_server_ciphers on;
# Security header
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains" always;
# Proxy to the local n8n process
location / {
proxy_pass http://localhost:5678;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-Proto $scheme;
}
}
EEFA note: If n8n runs on plain HTTP, keep proxy_set_header X-Forwarded-Proto https; to avoid mixed‑content warnings in the UI.
Why it matters: without the header the browser still tries HTTP assets, breaking the UI for some users.
1.2 IP allow‑list (n8n)
Restrict inbound traffic to known corporate ranges using the host firewall.
# Allow only the corporate subnet (example) sudo ufw allow from 203.0.113.0/24 to any port 443 comment 'Enterprise IP range' sudo ufw enable
Zapier Enterprise offers the same via a UI setting—no code.
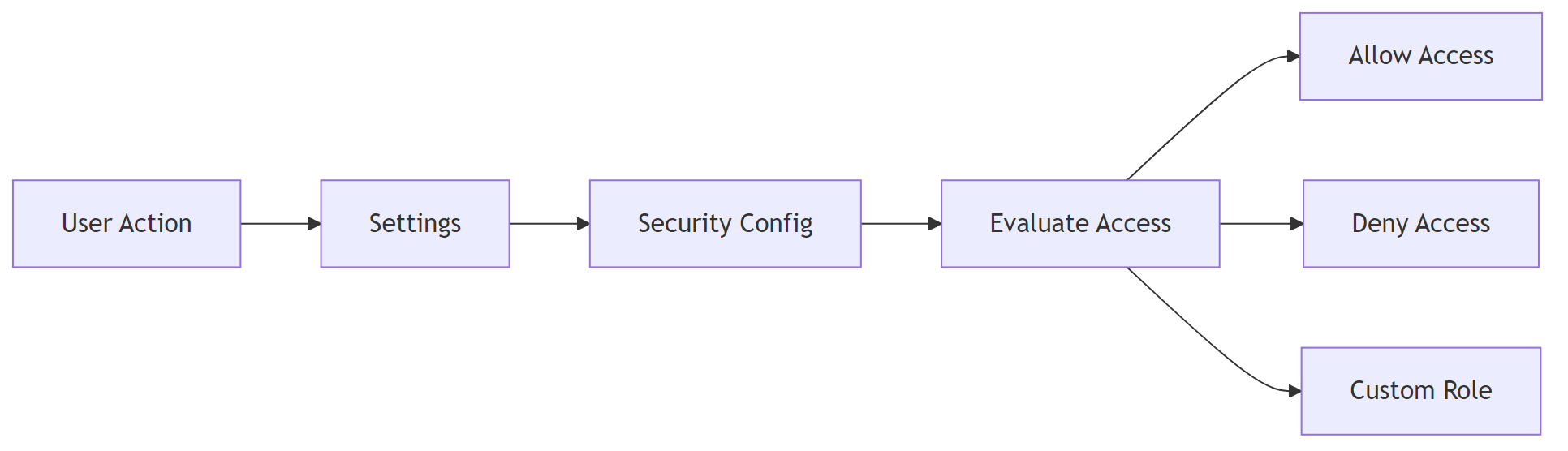
2. Identity & Access Management
If you encounter any n8n vs zapier features comparison resolve them before continuing with the setup.
Purpose: ensure only authorized users can log in and act on workflows.
2.1 SAML SSO configuration (n8n)
- Navigate to Settings → Security → SAML.
- Paste the IdP metadata URL.
- Map the IdP NameID to the n8n user email.
- Enable Just‑In‑Time provisioning for auto‑creation.
# n8n.config.yml – SAML endpoint & certificate
saml:
entryPoint: "https://idp.example.com/saml2/idp/SSOService.php"
issuer: "https://n8n.example.com/"
cert: |
-----BEGIN CERTIFICATE-----
MIID...
-----END CERTIFICATE-----
# Attribute mapping – email claim
attributeMapping:
email: "http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress"
EEFA: The cert must be PEM‑encoded with line‑breaks ≤64 chars; otherwise n8n rejects the SAML response.
2.2 Role‑Based Access (n8n)
| Role | Permissions | Typical use‑case |
|---|---|---|
| Owner | Full admin, workflow CRUD, credential mgmt | Platform admins |
| Editor | Create/modify workflows, no credential delete | Power users |
| Viewer | Execute workflows, read‑only access | Auditors, compliance officers |
Create custom roles via the UI (Settings → Users → Roles) or the API:
# Create a role (API call) curl -X POST https://n8n.example.com/api/v1/role \ -H "Authorization: Bearer $ADMIN_TOKEN" \ -H "Content-Type: application/json" \
{
"name":"Auditor",
"permissions":["workflow:read","execution:read"]
}
Zapier Enterprise supplies predefined team and admin roles but no custom permission sets.
In practice, if you need a role that only views logs, a custom n8n role is usually quicker than working around Zapier’s fixed groups.
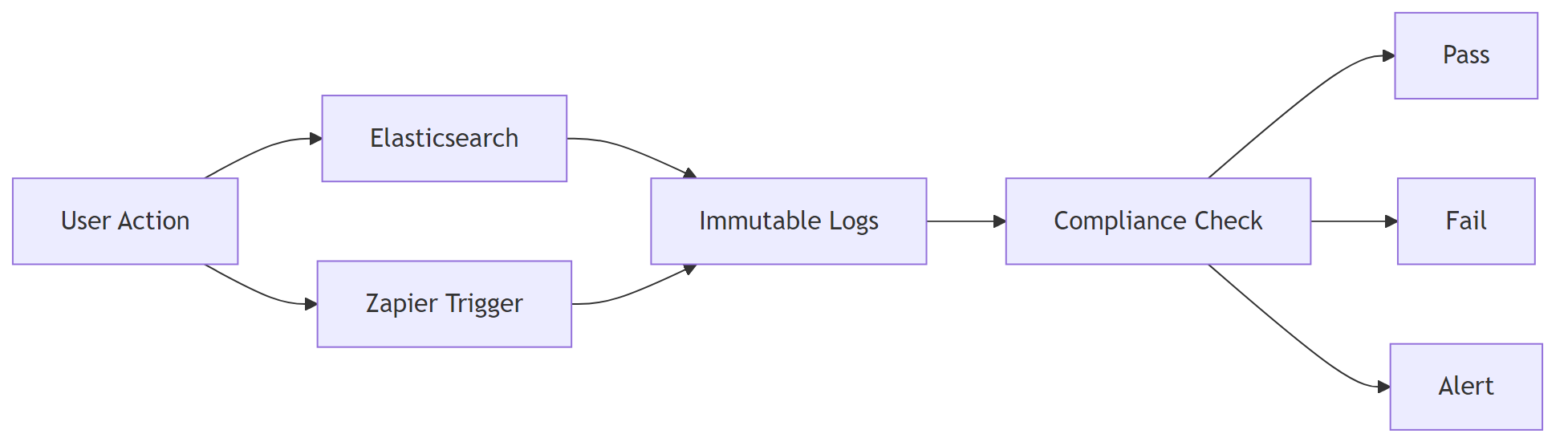
3. Data Governance & Auditability
If you encounter any n8n vs zapier performance scaling resolve them before continuing with the setup.
Purpose: capture immutable execution records for forensic and compliance purposes.
3.1 Immutable execution logs (n8n)
Deploy Elasticsearch with a write‑once index lifecycle policy.
# elasticsearch.yml – enable ILM index.lifecycle.name: immutable_policy index.lifecycle.rollover_alias: n8n-logs
# Policy definition – 30‑day rollover, 365‑day retention
PUT _ilm/policy/immutable_policy
{
"policy": {
"phases": {
"hot": { "actions": { "rollover": { "max_age": "30d" } } },
"delete": { "min_age": "365d", "actions": { "delete": {} } }
}
}
}
# Push a workflow execution to Elasticsearch curl -X POST http://elasticsearch:9200/n8n-logs/_doc \ -H "Content-Type: application/json" \ -d '@execution.json'
EEFA: Verify the delete phase matches your retention policy; otherwise logs could be removed early.
3.2 Zapier event‑log export
Zapier Enterprise lets you export Task History as CSV (max 90 days). For longer retention, forward each completed task to a SIEM:
- Create a Zap with Trigger: “Zapier Task Completed”.
- Action: Webhooks → POST → your SIEM endpoint.
Limitation: Zapier does not provide a native immutable log; durability depends on downstream storage.
4. Compliance Matrix
| Standard | n8n (self‑host) | Zapier (Enterprise) | Implementation guidance |
|---|---|---|---|
| SOC 2 Type II | (requires your own audit) | (provided) | Engage a CPA to audit your deployment for n8n. |
| ISO 27001 | (if you align infra) | (provided) | Map controls to ISO Annex A; document in your ISMS. |
| HIPAA | (with encrypted storage & audit logs) | (not offered) | Use encrypted EBS volumes and enable CloudTrail‑style logging. |
| GDPR | (data residency, DPA) | (EU data centers) | Sign data‑processing agreements for both platforms. |
| PCI‑DSS | (with network segmentation) | (Zapier not PCI‑validated) | Deploy n8n behind a PCI‑validated firewall; mask card data. |
EEFA: Audits are only as strong as surrounding processes—keep documented change‑management, credential rotation, and incident‑response playbooks for either tool.
5. Secret & Credential Management
Purpose: store API keys and other secrets safely, avoiding plaintext in config files.
5.1 n8n – External secret store integration
Reference secrets from HashiCorp Vault (or AWS/Azure equivalents) inside the n8n config.
# n8n.config.yml – AWS credentials via Vault
credentials:
- name: "aws"
type: "aws"
data:
accessKeyId: "{{ vault('aws/access_key_id') }}"
secretAccessKey: "{{ vault('aws/secret_access_key') }}"
EEFA: Set VAULT_ADDR and VAULT_TOKEN as env vars; never hard‑code tokens in the config file.
5.2 Zapier – Encrypted API keys
Zapier stores API keys in an internal encrypted vault. To rotate a key:
- Open My Apps → Edit for the relevant integration.
- Click Regenerate.
- Zapier flags any Zaps that lose their connection, prompting a quick fix.
Zapier does not expose a secret‑rotation API, so rotation must be manual.
6. Checklist: Enterprise Security Readiness
| Item | Platform | How to verify |
|---|---|---|
| TLS 1.2+ enforced | n8n / Zapier | openssl s_client -connect <host>:443 -tls1_2 |
| SAML/SSO enabled | n8n / Zapier | Log in via IdP; inspect SAML response in browser dev tools |
| IP allow‑list active | n8n / Zapier | curl -I https://<host> from an unauthorized IP – should be blocked |
| Immutable audit log | n8n | Query Elasticsearch index for tamper‑evidence |
| SOC 2 compliance proof | Zapier (certificate) | Request SOC‑2 report from Zapier sales |
| Secret rotation process documented | Both | Review SOPs; test rotation on a non‑critical credential |
| Data residency confirmed | Both | Verify cloud region in Zapier admin console; check VM location for n8n |
Many teams discover a missing IP allow‑list during a post‑mortem; double‑check early.
7. When to Choose n8n vs Zapier for Enterprise Security
| Decision factor | Choose n8n | Choose Zapier |
|---|---|---|
| Control over infrastructure | ✔️ Self‑hosted, custom firewalls, on‑prem | ❌ SaaS only |
| Regulatory audits requiring full log control | ✔️ Custom audit‑log pipeline | ❌ Limited log granularity |
| Speed of onboarding | ❌ Requires infra provisioning, cert management | ✔️ Immediate SaaS access |
| Budget for security tooling | ✔️ Leverages existing vault, SIEM | ❌ Additional Zapier Enterprise license |
| Future‑proofing for new standards | ✔️ You can add any compliance audit | ❌ Must wait for Zapier product updates |
Conclusion
Both platforms can satisfy enterprise security needs, but they solve different problems. n8n gives you full control over infrastructure, audit logs, and secret management essential when regulations demand custom compliance evidence or on‑premise data residency. Zapier removes the operational burden by delivering a managed SaaS with built‑in SOC 2 coverage, at the cost of reduced granularity and flexibility.
Pick the solution that aligns with your organization’s risk tolerance, compliance timeline, and operational capacity, and follow the checklist above to validate that your chosen automation platform meets the required security, compliance, and governance standards in production.